Discover why Vitrium stands out as the superior DRM software choice for content protection with seamless access, robust ...

Protect Your Content & IP With DRM Software
Distribute Content Securely & Easily
Choose from various DRM solutions.
Vitrium Pro
Your protected content can be shared directly with authorized end users via a secure web viewer, streaming on-demand, or a customized user portal.
Vitrium Enterprise
Your protected content can be distributed through a 3rd party system such as an LMS, CRM, AMS, eCommerce, or other system through API integration.
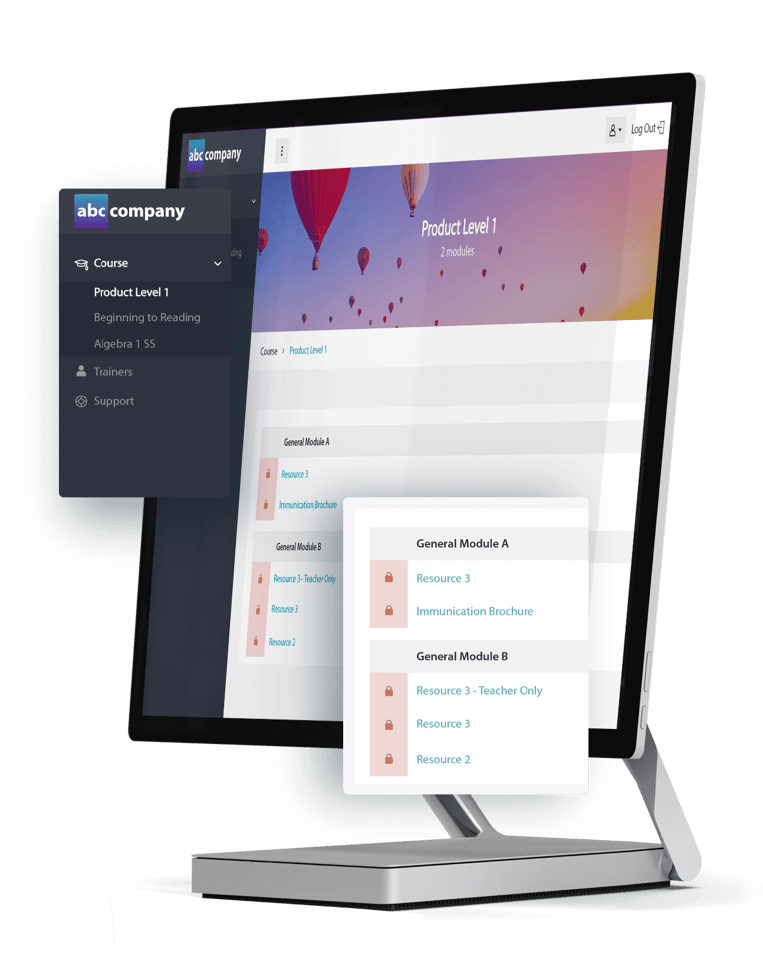
VitriumOne
Your protected content can be distributed to schools, customers or partners who can redistribute content to their teachers, students or users.
If you’re unsure which solution is right for you,
Whatever solution you choose, Vitrium DRM gives you complete control over your content.

Strong Protection & Encryption
When you upload your content in Vitrium, it gets protected with AES encryption. With numerous DRM options at your control, you can choose whether to allow or prevent printing, copying, downloading or screen sharing. You can also add dynamic user-identifying watermarks.
Seamless User Access
Vitrium does not require any plug-ins or apps. Content is quick and easy to access. The Vitrium Viewer includes extensive annotation capabilities for documents and images. The Vitrium Video Player supports different bitrate streams and the ability to add bookmarks.
Secure Content Distribution
Share content with authorized users. Start as simple as copying a web link in an email. Or distribute content via a custom user portal. Or connect Vitrium to a 3rd party system to automate your workflows and offer users single sign-on (SSO) access with this system.
Tracking & Analytics
Gain valuable insight into how your users are accessing and consuming content. Identify who is accessing your content, when and how. Learn what your top performing content is, who your most active users are, and make informed decisions based on this.
Protect Multiple File Formats With Vitrium!
Vitrium’s DRM software allows you to protect documents, images, audio and videos. Vitrium encrypts these formats with 128-bit AES encryption and converts them to a secure web format.

Vitrium solutions provide the optimal balance between content protection and user experience.
Read more in our white paper.
Download a copy today.

“With the need to go online for class delivery, Vitrium enables us to protect the IP of our teaching & learning materials.“
“If you have to choose between Vitrium and another company, I suggest going with Vitrium. We have peace of mind knowing our valuable intellectual property is protected with Vitrium.”
“Vitrium is easy to use and has a high level of customization. It is constantly evolving to a better product.”
Vitrium DRM is used by companies around the world!
Read our case studies to learn more.
WPS in the USA uses Vitrium Security Enterprise to protect their educational and psychological assessments. This ensures their sensitive content is secure but still easily accessible by their users.
IVES Training in Canada uses Vitrium Security Enterprise to protect their training eBooks and videos, ensuring their valuable IP is protected. They've integrated Vitrium with their CRM system.
LivCor uses VitriumOne to protect valuable First Aid educational materials that are distributed through their network of partners in the Australian market.
Recent blog posts
Discover how Vitrium DRM debunks common myths about digital rights management by delivering strong content protection wi...
Discover why DRM software is the future of secure content distribution, offering stronger protection than passwords, sha...
A major Canadian standards organization has relied on Vitrium since 2017 to protect over 80 thousand standards documents...
Our new Admin Notifications feature enables content distributors to receive timely alerts when certain events happen on ...
After a year full of dedication and hard work, we've decided to round up the top 10 features we released in our DRM soft...
“ Both the Vitrium product and team have been a pleasure to work with. We pose an unusual case and Vitrium has been exceptionally accommodating and helpful. ”
Ease the stress of sharing sensitive and valuable content.
CONTACT US
© Copyright 2025 Vitrium Systems Inc.





