Vitriun enables its users to protect Excel files with DRM software. Explore this article to learn the different ways Excel files can be protected & shared with DRM.
What Happens After You Share A File Using Vitrium's DRM?
Sharing digital files is easy. Understanding what happens after you hit “send” is not.
For organizations handling sensitive documents, training materials, intellectual property, or paid content, the real risk doesn’t come from sharing, it comes from losing visibility and control once the file leaves your system.

What Usually Happens After a File Is Shared
With standard file-sharing tools (email attachments, cloud storage links, downloads, etc.) and even when some level of protection is added to your digital content (passwords, Google/OneDrive permissions, manual watermarking, etc.) files behave in predictable and risky ways:
-
Files can be forwarded to unintended recipients
-
Copies can be downloaded, saved, and/or duplicated
-
Access can continue even after a user leaves the organization
-
You lose visibility into who opened the file, when, and how often
-
Revoking access after sharing is often impossible
Once a file is downloaded or shared externally, control is mostly gone.
This is where many organizations ask:
“What’s actually happening with our files after they’re shared?”
Why Does Tracking Matters?
Knowing what happens to your files after distribution isn’t just about security, it’s about accountability, compliance, and business insight.
Without tracking and controls, you’re relying on trust, not data. Post‑sharing visibility helps you:
-
Detect unauthorized access or suspicious behavior
-
Confirm how the content is being viewed, for how long or if it is ignored altogether
-
Meet regulatory and audit requirements
-
Protect revenue‑generating or proprietary materials
-
Respond quickly when access needs to change
How Vitrium DRM Shows You What Happens After Files Are Shared?
Vitrium DRM protects files beyond the moment of sharing, giving you continuous visibility and control.
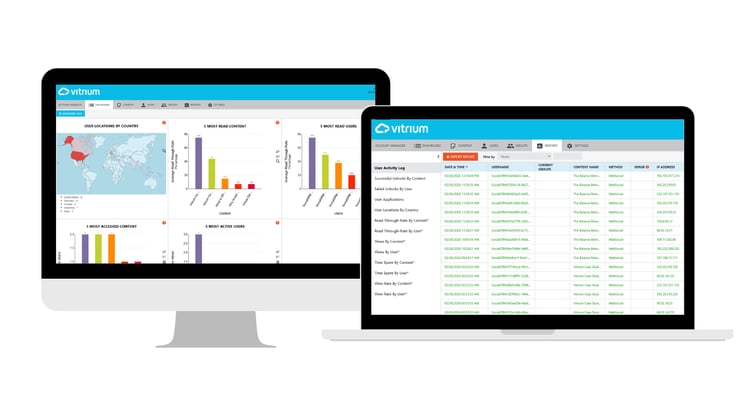
1. Real‑Time Access Tracking
With Vitrium, every protected file generates actionable insights:
-
View activity by user or group
-
Track when files are opened and how often
-
Monitor geographic access patterns
-
Identify inactive or over‑shared content
This transforms files from static assets into measurable digital interactions.
2. Persistent File Protection
Unlike traditional sharing methods, Vitrium embeds protection directly into the file itself.
That means:
-
Security stays with the document, even if it’s forwarded
-
Access rules apply wherever the file goes
-
Unauthorized users are blocked automatically
Protection doesn’t stop at the link, it travels with the content.
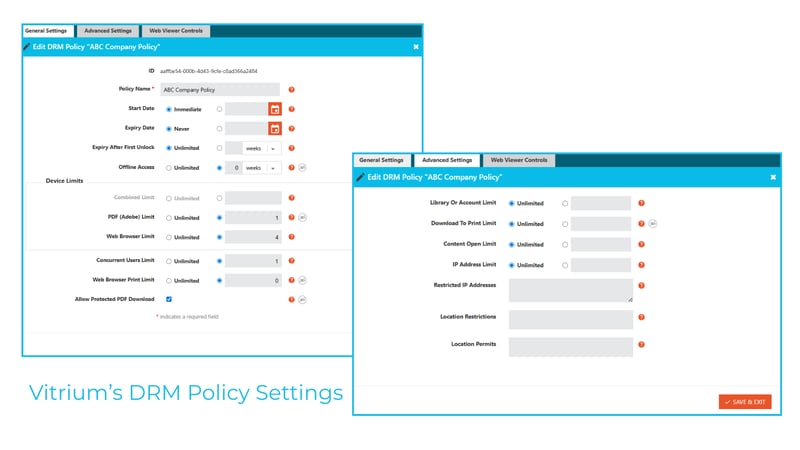
3. Granular Access Controls
Vitrium lets you define exactly how content can be used after sharing:
-
View‑only or downloadable access
-
Time‑based expiration
-
User‑ or group‑specific permissions
-
Control printing, copying, and screen capture
And most importantly, you can change these rules at any time, even after the file has been distributed.
4. Instant Access Revocation
If access should change, Vitrium makes it immediate:
-
Remove access for a single user
-
Disable a file globally
-
Update permissions without re‑sharing
This is especially critical for when:
-
Employees leave
-
Contracts expire
-
Content becomes outdated
-
A security incident occurs
No recalls. No re‑uploads. No guesswork.
5. Compliance‑Ready Audit Trails
For organizations operating under compliance frameworks, Vitrium provides:
-
Detailed access logs
-
User‑level activity records
-
Centralized reporting
This supports audits, investigations, and governance requirement but without manual tracking.
What This Means for Your Business
When you know what happens to your files after they’re shared, you can:
-
Protect intellectual property without slowing collaboration
-
Confidently share content with partners and customers
-
Make data‑driven decisions about content usage
-
Reduce risk without increasing operational complexity
Vitrium DRM doesn’t just protect files, it connects content with insight.

Protect Your Content. Protect Your Business.
Protecting digital content doesn’t have to be a chore. The key is adopting a DRM strategy that balances strong security with minimal friction. With the right solution in place, one that supports effortless access, integrates with your systems and scales across formats, you get the peace of mind that your assets are safe and the usability that your users expect.
Want to explore how hassle-free DRM looks in action? Feel free to reach out, speak with our team, or explore our platform. Your content deserves protection, without compromise.